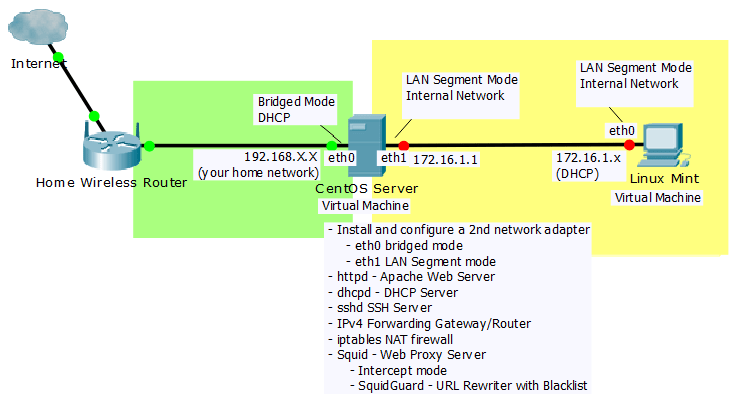
From a networker’s perspective there is so much you can do with Linux, so many servers and free tools to play with. Linux can be a server, a gateway router, a proxy, a transparent bridge you name it, and using virtualization I have the flexibility to test things from my laptop workstation.
The idea for this lab was taken from my Winter 2015 Final Exam, it is a great project that I know you will love. I have updated it to work with CentOS7.
Lab Instructions:
//*******************************************\\
CentOS7 Linux Router and Server
\\*******************************************//
====================
Install Linux - 2pts
====================
A. Use the CentOS7 minimal install x86_64 iso image file. You can download it here: http://centos.org/
B. Using Virtualbox create a new virtual machine: Choose “I will install the operating system later.”
- Settings: Linux, RedHat 64 bit, Disk Size minimum 12Gb, Memory 1 to 2Gb
- Choose Settings: set the CD-ROM to boot directly from the CentOS-7 iso image file,
- Choose Settings: set the network adapter to bridged mode
C. Click finish and then Start which will boot the virtual machine to the iso image file. Install CentOS-7.5 (the latest version)
D. Important settings:
- Name your Centos localhost hostname <centos.yourname.local>
- set the root password <yourchoice>
- create a user account and password
- set the location timezone
- accept all other default settings
E. Login to CentOS7 as root and take a screenshot logged into your CentOS7 Virtual Machine (save screenshot)
======================================
Add and Configure 2 Network Adapters - 2pts
======================================
1. Starting with CentOS-7 minimal install and virtual machine network interface in bridged mode
2. # ip addr //have you picked up an ip address from the network DHCP server? If not, try:
# ifdown enp0s3
# ifup enp0s3
3. Next, you will manually edit/configure the ifcfg-enp0s3 network adapter configuration file:
# cd /etc/sysconfig/network-scripts
# ls # vi ifcfg-enp0s3
- using vi press “i” for insert mode
- to save press “esc”, then type a “:”, then “wq” to write quit
- make sure the configuration has the following items you do not need to delete any other items:
DEVICE=enp0s3
HWADDR=<mac-address> //adding this is optional, see network adapter advanced settings in Virtualbox for the virtual NIC mac address
TYPE=Ethernet
ONBOOT=yes
NM_CONTROLLED=no //**this is the only line we need to add
BOOTPROTO=dhcp
# ifup enp0s3
- if needed
# ifdown enp0s3
# service network restart
4. Once you are online install the following tools:
# yum install nano
# yum install vim
# yum install wget
# yum install openssh
# yum install iptables-services
# yum install net-tools
# yum install bridge-utils
5. Now that eth0 is working and you are connected online it is time to shutdown your system
and install a second network interface card.
# shutdown -h now
- edit your virtual machine’s Settings:
- Settings: select Network > select Adapter 2:
- Activate Network Adapter: checkmarked,
- Attached to: Internal Network,
- Name: vlan
- Advanced > Promiscuous Mode: Allow all
- ” > cable connected: checkmarked
6. Start Centos7 and check to see if CentOS7 recognizes the new network adapter:
# ifconfig -a |less
- if enp0s8 shows up, then go to step 7.
- if enp0s8 doesn’t show up, then shutdown CentOS, go back to virtual machine settings
- deactivate the network adapter 2 and then re-enable it.
- if enp0s8 still doesn’t show up, then go to step 7 anyway and try and force it to see it.
7. Copy ifcfg-enp0s3 to ifcfg-enp0s8 to create a configuration file for enp0s8:
# cp /etc/sysconfig/network-scripts/ifcfg-enp0s3 /etc/sysconfig/network-scripts/ifcfg-enp0s8
8. Edit ifcfg-enp0s8
# nano /etc/sysconfig/network-scripts/ifcfg-enp0s8
DEVICE=enp0s8
HWADDR=<mac-address> //see network adapter advanced settings
TYPE=Ethernet
IPADDR=172.16.1.1
NETMASK=255.255.255.0
ONBOOT=yes
NM_CONTROLLED=no
BOOTPROTO=none
# ifup enp0s8
- if needed
# ifdown enp0s8
# service network restart
9. Take a screenshot showing your active enp0s3 and enp0s8 interfaces.
# ifconfig -a |less //take screenshot
=========================================================
Install Apache Webserver and reach it from your Windows computer - 2pts
=========================================================
1. # yum install httpd //install apache web server
# systemctl start httpd //start the apache web server
# systemctl enable httpd //set it to run on startup
# nano /var/www/html/index.html //create and edit a simple index.html homepage
<html>
<head><title>Welcome to my “Your Name” Homepage Final</title>
</head>
<body>
Hello this is my webserver homepage!
</body>
html>
2. In this lab we will use the older iptables instead of the newer nftables(firewalld). You will need to shutdown the nftables firewall in order to reach the Apache webserver
# systemctl stop firewalld
# systemctl disable firewalld
3. Using your hsot computer (not CentOS7) open a web browser, and browse to your CentOS7 web server’s enp0s3 ip address
4. Take a screenshot of your Apache web server homepage from the Web Browser
=====================================
Install and configure a DHCP server - 2pts
=====================================
1. # yum install dhcp //install dhcp server
# systemctl start dhcpd //the dhcpd service should fail because it has not been configured yet
# systemctl enable dhcpd //set it to run on startup
3. Configure the dhcp server
# cd /etc/dhcp/
# ls
# nano /etc/dhcp/dhcpd.conf
subnet 172.16.1.0 netmask 255.255.255.0 {
range 172.16.1.100 172.16.1.150;
option domain-name-servers 8.8.4.4, 4.4.2.2;
option routers 172.16.1.1;
option broadcast-address 172.16.1.255;
}
4. # service dhcpd restart
Note: if it fails the dhcpd.conf file has errors that need to be fixed,
or your enp0s8 interface is not enabled with the correct ip address
5. From another virtual machine (Linux Mint VM) with the virtual network adapter set to Internal Network (name: vlan) try picking up an ip address from the CentOS7 DHCP server by setting the local area connection to automatically pick up an IP address (DHCP client)
6. Take a screenshot showing a successful dhcp address lease on a virtual machine using the same Internal Network as the CentOS7 Server. Open a command prompt and issue an ipconfig, or from the Centos Server use the following command to check for dhcp leases:
# cat /var/lib/dhcpd/dhcpd.leases
=================================================
SSH into your server from Windows using PuTTY - 2pts
=================================================
1. Install the Windows PuTTY client to your Windows computer
2. In Centos check to see of SSHD is already started, if not start it
# service sshd status
# service sshd start
3. If you did not create a user account when you installed CentOS7 then you will want one:
# adduser
# passwd
<enter a password of your choice>
<re-enter the password>
4. In Windows open PuTTY, put the ip address of CentOS (enp0s3), click Open and enter your name and password.
5. Take a screenshot of your successful SSH connection.
===============================
IP Forwarding and Iptables - 2pts
===============================
1. Turn on routing in the kernel by setting net.ipv4.ip_forward = 1
# sysctl -w net.ipv4.ip_forward=1
- to make the setting survive a reboot add the setting to the sysctl.conf file
# nano /etc/sysctl.conf
- add the following line, save and quit
net.ipv4.ip_forward = 1
2. Load the new sysctl settings
# sysctl -p
3. Configure iptables firewall rules and nat by creating a firewall script to load the configuration commands
# cd /usr/local/bin
# touch firewall_script
# chmod 700 firewall_script
# nano firewall_script
4. Below is the firewall_script line by line:
#!/bin/bash
# Basic firewall script
# Define variables
ipt=”/sbin/iptables”
int_intf=enp0s8
ext_intf=enp0s3
# Flush all active rules and delete all custom chains
$ipt -F
$ipt -t nat -F
$ipt -t mangle -F
$ipt -X
$ipt -t nat -X
$ipt -t mangle -X
# Set default policies
$ipt -P INPUT ACCEPT
$ipt -P FORWARD ACCEPT
$ipt -P OUTPUT ACCEPT
$ipt -t nat -P OUTPUT ACCEPT
$ipt -t nat -P PREROUTING ACCEPT
$ipt -t nat -P POSTROUTING ACCEPT
$ipt -t mangle -P PREROUTING ACCEPT
$ipt -t mangle -P POSTROUTING ACCEPT
# This line is necessary for the loopback interface
# and internal socket-based services to work correctly
$ipt -A INPUT -i lo -j ACCEPT
# Enable IP masquerading (NAT)
$ipt -t nat -A POSTROUTING -o $ext_intf -j MASQUERADE
# Allow outside connections to servers
$ipt -A INPUT -p tcp -dport 22 -sport 1024:65535 -m state -state NEW -j ACCEPT
$ipt -A INPUT -p tcp -dport 80 -sport 1024:65535 -m state -state NEW -j ACCEPT
# Enable unrestricted outgoing traffic, incoming traffic
# is restricted to locally-initiated sessions only
$ipt -A INPUT -i $ext_intf -m state -state ESTABLISHED,RELATED -j ACCEPT
$ipt -A INPUT -i $int_intf -m state -state NEW,ESTABLISHED,RELATED -j ACCEPT
$ipt -A FORWARD -i $ext_intf -o $int_intf -m state -state ESTABLISHED,RELATED -j ACCEPT
$ipt -A FORWARD -i $int_intf -o $ext_intf -m state -state NEW,ESTABLISHED,RELATED -j ACCEPT
# Accept important ICMP messages
$ipt -A INPUT -p icmp -icmp-type echo-request -j ACCEPT
$ipt -A INPUT -p icmp -icmp-type time-exceeded -j ACCEPT
$ipt -A INPUT -p icmp -icmp-type destination-unreachable -j ACCEPT
# Reject connection attempts not initiated from inside the LAN
$ipt -A INPUT -p tcp -syn -j DROP
# Send LAN web requests to Squid,
# the line below is commented out at first until Squid is installed and configured
#$ipt -t nat -A PREROUTING -i $int_intf -p tcp -dport 80 -j DNAT -to 172.16.1.1:3128
5. Start iptables then run your script to configure iptables
# service iptables start
# ./firewall_script //if errors exist fix script, save, and run script again
6. Take a screenshot of your firewall script and another of your firewall running successfully
# service iptables status
===============================
Install and configure Squid - 2pts
===============================
1. Install Squid
# yum install squid
# systemctl start squid
# systemctl enable squid
# nano /etc/squid/squid.conf
//since this is now a transparent proxy, on line 62 edit the following line to read
http_port 3128 intercept
# systemctl restart squid //or reload
2. Open up your WindowsXP Pro client, behind your Centos Server (LAN Segment VLAN10) and open a browser to test to see if Squid is intercepting web requests
# tail -f /var/log/squid/access.log
3. Take a screenshot of the Squid access log
==========================================
Install and configure squidGuard - extra credit 2pts
==========================================
1. Install squidGuard, you need the epel repositories
# yum install epel-release
# yum install squidGuard
2. Configure Squid to use squidGuard:
# nano -c /etc/squid/squid.conf
// add the following line around line 26:
url_rewrite_program /usr/bin/squidGuard
# systemctl restart squid
3. Make a blacklists directory in squidGuard
# mkdir /var/squidGuard/blacklists
//download a publicly available blacklist file to /usr/local/bin using wget or you could do a testdomains page instead of a full blacklist
# cd /usr/local/bin
# wget http://www.shallalist.de/Downloads/shallalist.tar.gz
//extract the compressed blacklist file, then copy the folder named “gamble” to the blacklists folder
//the file extracts into a folder named “BL” and within that folder are the blacklist categories
# tar -xvf shallalist.tar.gz
# ls
# cd BL
# cp -R gamble /var/squidGuard/blacklists
4. Configure squidGuard:
# nano -c /etc/squid/squidGuard.conf
//edit the squidGuard.conf file starting at line 33 with the following changes:
//comment out the user line shown below in the “src admin” block with a “#”
//comment out all the lines in the “dest adult” block with a “#” in front of each line
src admin {
ip 1.2.3.4 1.2.3.5
# user root foo bar //don’t forget to comment this out
within workhours
}
#dest adult {
# domainlist blacklists/…
# urllist blacklists/…
# expressionlist blacklists/…
# redirect http://admin…
#}
dest gamble { //add this dest gamble block
domainlist gamble/domains //…add
urllist gamble/urls //…add
} //…add
acl {
admin {
pass any
}
foo-clients within workhours {
# pass good !in-addr !adult any //comment out this line with a “#”
} else {
pass any
}
bar-clients {
pass local none
}
default {
pass !gamble any //change this line to “pass !gambling any”
rewrite dmz
redirect http://172.16.1.1/blocked.html //change to redirect to your own blocked webpage
}
}
5. Add draftkings.com to your gambling blacklist (or any other domains you want to block)
# nano -c /var/squidGuard/blacklists/gamble/domains
// add a line at the top of domains for draftkings.com (you can add more test domains to block also)
6. Compile the squidGuard database files, then chown the entire blacklists folder and files
# squidGuard -b -d -C all
# chown squid:squid -R /var/squidGuard/blacklists
7. Reload Squid
# systemctl restart squid
7. Go to the Linux Mint or Windows virtual machine on the internal network vlan10
and open a browser to test to see if Squid is using squidGuard to block unsavory websites.
If you cannot web browse to a gambling domain listed in the gamble/domains file then squidGuard is working.
// run an ongong tail command on the LAN segment host # tail -f /var/log/squid/access.log
8. Create a blocked.html file by copying your index.html file
# cp /var/www/html/index.html /var/www/html/blocked.html
9. Edit the blocked.html file content to read, “You are blocked!”
# nano /var/www/html/blocked.html
//you should now see your blocked.html page everytime squidGuard blocks a web site or domain
10. Take a screenshot of a successful blocked page result from the virtual machine client (Mint or Win) on the internal network (vlan)
Video Walkthrough
Part 1
Part 2
Part 3
Part 4
Part 5
Part 6
Part 7
